Anthropic has just launched Claude Code Security, an AI security tool that has already detected more than 500 high-severity vulnerabilities in open source projects. Flaws that have eluded human experts for decades. Here's everything you need to know to protect your organization's code bases with this new cybersecurity weapon.
What is Claude Code Security and why is it a turning point for software security
Claude Code Security is a new feature integrated into Claude Code on the web. Launched by Anthropic in February 2026, it makes it possible to scan entire code bases in search of vulnerabilities, then to suggest targeted patches submitted for human review. In short, it's an AI security tool designed to do what traditional scanners can't: reason about your code.
The initial observation is simple. Security teams are overwhelmed. Vulnerability backlogs keep growing. And traditional static analysis tools, as useful as they are, are limited to detecting patterns that are already known. They are good at identifying hard passwords or outdated encryption. But as soon as we talk about business logic flaws, poorly implemented access control, or vulnerabilities that arise from the interaction between several components, they miss out.
This is exactly where Claude Code Security is changing the game. Instead of comparing code to a signature database, this AI security tool reads and reasons on the code as a human security researcher would. It traces the flow of data through the files. It understands how components interact with each other. And it identifies complex logical errors that rule-based tools simply don't see.
The figure that made the entire cybersecurity sector react: Claude Opus 4.6, the model that powers the tool, identified more than 500 high-severity vulnerabilities in widely used open source libraries such as Ghostscript, OpenSC and CGIF. These bugs had been around for decades. Years of review by human experts had not spotted them.
For the moment, Claude Code Security is available in a limited research preview. The customers Anthropic Enterprise and Team can request access. Maintainers of open source projects benefit from accelerated and free access. Anthropic clearly wants to put this capability in the hands of defenders first and foremost, before attackers benefit from the same advances.
What types of vulnerabilities does Claude Code Security detect
The strength of Claude Code Security lies in the depth of its code analysis. The tool doesn't just look for known patterns. He understands the code, and it is this understanding that allows him to detect categories of flaws that traditional scanners systematically lack.
Memory corruption and buffer overflows
Memory corruption vulnerabilities are among the most dangerous in software security. A buffer overflow can allow an attacker to crash a system or even execute arbitrary code. Claude Code Security excels in detecting this type of vulnerability because it is not limited to looking for risky function calls. It understands the logic behind the code.
The most obvious example comes from the CGIF library, a tool for processing GIF files. Claude discovered a heap buffer overflow vulnerability that required a detailed understanding of the LZW algorithm and its relationship with the GIF format to be triggered. The crucial point: even with 100% test coverage of lines and branches, this vulnerability could have remained invisible. It required a very specific sequence of operations that only contextual reasoning could identify.
In the case of OpenSC, a smart card processing utility, Claude identified a buffer overflow by looking for function calls like strrchr () and strcat () and by understanding how these functions interacted in the specific context of the code. This type of code analysis goes far beyond what a rule-based scanner does.
Injection flaws and authentication bypass
Injection flaws remain one of the most common threats in software security. SQL injection, command injection, or template injection: these vulnerabilities occur when an application does not properly filter user input. Claude Code Security identifies code portions that lack effective filters, even when the pattern is not classical.
The tool also detects authentication bypasses, these flaws that make it possible to bypass the authentication mechanisms of an application. The security analysis that Claude carries out goes beyond verifying the presence of an authentication module. It looks at how this module interacts with the rest of the application, and whether unprotected paths exist.
What makes this detection particularly effective is that Claude reasons about the complete flow of a request through the application. It does not look at each file in isolation. It traces the data journey from end to end.
Complex logic errors and access control flaws
This is undoubtedly the area where Claude Code Security distinguishes itself most clearly from traditional tools. Complex logic errors do not correspond to any known signature. They come from the way a developer implemented a feature, not from an identifiable code pattern.
For example, an access control system may look good in each file individually, but be flawed when you understand how the components fit together. Claude Code Security tracks how data flows through the entire codebase. It includes interactions between modules. And it identifies cases where business logic creates unintended breaches.
However, one important limitation should be noted. Claude Code Security does static code analysis, although it is much smarter than traditional static analysis. It does not launch the application. It cannot therefore confirm that a vulnerability is really exploitable in a given production environment. Runtime validation is still required for a complete security review.
How does Claude Code Security work: from scan to patch
Understanding the inner workings of Claude Code Security allows you to understand why this AI security tool is different from existing solutions. The process takes place in several steps, from connecting to your code repository to getting the patches approved by your team.
Contextual reasoning, not pattern matching
The security analysis carried out by Claude Code Security is based on a principle that is fundamentally different from classical static analysis. Traditional tools work by pattern matching: they compare your code to a database of known vulnerabilities. If your code looks like a dangerous pattern, it's reported. This approach works for common flaws, but it misses anything out of the catalog.
Claude Code Security, on the other hand, reasons about your code. It can read a project's Git history to understand what changes introduced bugs. It traces data flows through files to identify where unfiltered input could be a problem. He understands business logic well enough to know what specific input could break a given function.
It was exactly this ability to analyze contextual code that allowed Claude to discover the flaw in Ghostscript. After classical fuzzing and manual analysis came to nothing, Claude turned to the project's Git history, identified a commit that introduced a bug related to a missing terminal check, and then proactively checked to see if similar bugs existed elsewhere in the codebase.
Multi-stage adversarial verification
One of the major problems with traditional security analysis tools is the false positive rate. When a tool reports 200 vulnerabilities, half of which aren't, vulnerabilities, teams waste precious time triaging. Claude Code Security addresses this problem head-on.
Each vulnerability detected goes through an adversarial verification process. Concretely, Claude is questioning his own discoveries. It attempts to prove or disprove each result before presenting it to an analyst. This process acts as an internal filter that eliminates false positives in advance.
Validated vulnerabilities are then given a severity score so teams can prioritize. Claude also assigns a confidence index to each discovery. This dual scoring system helps teams focus their efforts on the most critical and certain issues, which greatly optimizes the security workflow.
Suggested fixes and mandatory human approval
Claude Code Security does not stop at detection. For each vulnerability identified, the tool offers a patch. A “suggest fix” button allows you to generate a patch that respects the structure and style of the existing code.
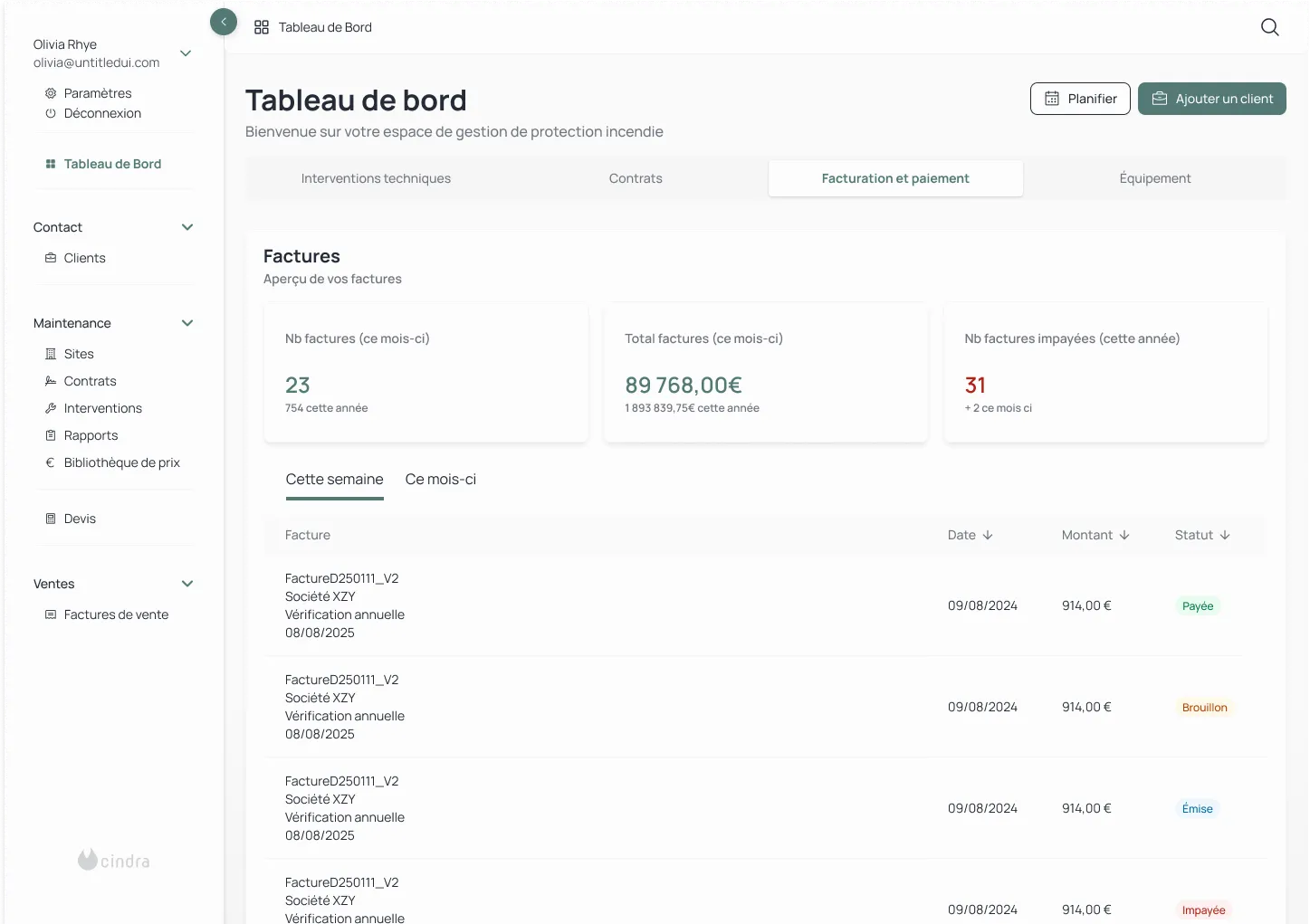
Validated results appear on the Claude Code Security dashboard, where teams can review them, inspect suggested fixes, and approve changes. This is an essential point: nothing is applied automatically. The developers are always in final control. Each patch requires human approval before it can be integrated.
This AI-assisted secure coding approach aims to accelerate remediation, not replace human judgment. Teams can also export the results to their existing vulnerability management tools, making it easy to integrate into an existing security workflow.
Claude Code's security architecture: permissions, sandbox and MCP protocol
When we talk about a tool that accesses your code bases, the question of its own security is legitimate. Claude Code was designed with a permission-based architecture that puts security first. Here's how.
Permissions-based architecture and bash command approval
Claude Code works in read-only mode by default. That is the starting point. Any action that goes beyond just reading, whether it's editing a file, running a command, or using an external tool, requires explicit user approval.
The bash command approval system is particularly rigorous. Even if an order is on the list of authorized commands, the system blocks it and asks for manual validation if suspicious behavior is detected. This command injection detection mechanism protects against cases where malicious input attempts to hijack Claude to execute destructive commands.
The principle of fail-closed matching further reinforces this code protection: any order that does not clearly correspond to a known authorization rule requires manual approval by default. Identifiers (API keys, tokens) are encrypted and stored securely. Claude Code's security documentation (security docs) details all of these mechanisms for teams who want to audit the system.
Sandboxing and secure execution in the cloud
Anthropic developed a sandboxing system for Claude Code that creates predefined boundaries within which the tool can work freely. This system is based on two pillars: file system isolation and network isolation.
File system isolation ensures that Claude can only access or modify specific directories. It cannot go and read your SSH keys or your identification files that are in other directories. Network isolation limits outgoing connections, preventing data exfiltration even if compromised.
For cloud execution security on the web, each Claude Code session runs in an isolated virtual machine managed by Anthropic. Authentication involves a secure proxy that uses a limited-range identifier in the sandbox and then translates it into your real GitHub credentials. Anthropic has also open-sourced this sandboxing technology so that other teams can adopt it in their own agents.
Model Context Protocol (MCP) security and tool governance
The Model Context Protocol (MCP) makes it possible to extend Claude Code's capabilities by connecting external tool servers. But this scalability comes with risks, and MCP security (mcp security) is taken seriously.
Each new MCP server requires a trust check before it can be used. Organizations can define enterprise-level allowlists and denylists to control which servers are authorized. These managed settings cannot be bypassed by individual developers, ensuring centralized governance.
The best practices recommended in the Claude Code Docs are clear: only activate trusted MCP servers, pin versions to avoid silent updates, and audit configurations regularly. Because an MCP server once approved can be updated without asking for new consent. Version pinning is therefore essential to maintain secure execution over time.
Claude Code Security versus traditional security tools: what's really changing
To fully understand what Claude Code Security brings, you must first understand how classical static analysis tools (SAST) work. These tools compare each piece of code to a database of rules that define known vulnerabilities. If a code snippet matches a pattern in the database, it is reported. This approach effectively detects common problems: hard-coded passwords, outdated encryption algorithms, or dependencies that are known to be vulnerable.
But these rules cannot cover all variants of all loopholes. They don't understand the context. They don't track data flows. And they often produce a high rate of false positives that end up drowning the real problems in noise. As a result, security teams spend more time triaging alerts than fixing real vulnerabilities.
Claude Code Security does not work the same way. Its security analysis is contextual. It understands how components of your application communicate with each other, how data flows from module to module, and why such implementation creates a risk. Adverse verification reduces false positives. And the automatic suggestion of fixes closes the loop between detection and remediation.
An important point: Claude Code Security is designed as a complement, not as a replacement. Anthropic makes it clear: the tool catches what conventional scanners lack, and you can export its findings to your existing security workflows. For complete code protection, it is part of a multi-layered approach where Claude's contextual analysis complements classical static analysis and runtime tests.
In fact, the market took this announcement very seriously. On launch day, the shares of several major cybersecurity companies fell significantly. CrowdStrike lost almost 8%, Cloudflare just over 8%. These stock market reactions show that the industry sees Claude Code Security not as a gimmick, but as a real paradigm shift in software security.
How to integrate Claude Code Security into your business
Moving from discovery to action is the next step. Here is how you can concretely adopt Claude Code Security in your development processes.
Who can access it and under what conditions
To date, Claude Code Security is available in a limited research preview. To access it, you must be an Anthropic customer with an Enterprise or Team plan. Maintainers of open source projects can request accelerated and free access. Anthropic wants to collaborate with the community to refine the capabilities of the tool before wider deployment.
An important condition of use: the tool can only be used on code that your company owns and on which it has all the necessary rights. No licensed third-party code, no open source projects that you don't maintain. This restriction is intended to regulate the responsible use of the tool.
Secure your daily use of Claude Code
Beyond the security scan functionality, it is essential to properly configure Claude Code itself for safe daily use. The recommended approach is to treat Claude Code as a powerful assistant but one that requires constant supervision. Any critical modification to your codebases must be subject to human review.
Permissions are configured in a granular manner via the managed-settings.json file. This file allows you to precisely define what Claude can do (allow), what requires approval (ask), and what is strictly forbidden (deny). The permissions-based architecture offers three levels of control that allow security to be adapted to the work context. Never run Claude Code with root privileges is an absolute rule. The tool must run in a sandbox environment, ideally a Docker container or a dedicated virtual machine, to limit the impact of a possible compromise.
Bash command approval should remain strict for sensitive operations. Resist the temptation to globally allow commands like git push or docker run. Prefer specific patterns (for example npm run test: *) that limit the scope of permissions. Audit authorized MCP configurations and servers on a monthly basis. And keep transcript retention short, between 7 and 14 days, to limit the exposure of sensitive data in the event of a leak.
Integrate Claude Code Security into your existing security workflow
Claude Code Security was designed to be integrated into the tools that teams already use. Because it's built on Claude Code, teams can review discoveries and iterate on fixes directly in their familiar environment.
Analysis results can be exported to existing vulnerability management systems. Anthropic's stated objective is to reduce the software security review process to a few clicks, while keeping humans in the loop for each critical decision. For organizations that already have a mature security workflow, Claude Code Security is added as an additional layer of code analysis that reinforces code protection without disrupting existing processes.
What Claude Code Security announces for the future of software security
The launch of Claude Code Security is part of a pivotal moment for cybersecurity. And Anthropic is fully aware of that.
The company says it openly: the same AI capabilities that help defenders find vulnerabilities can be exploited by attackers. It is the double edge of this technology. A model that can detect a zero-day vulnerability that has remained hidden for years is also a model that could, in the wrong hands, identify exploitable weaknesses more quickly than ever. Anthropic has also strengthened the security controls of Claude Opus 4.6 and put in place safeguards to detect and block malicious uses.
Anthropic's vision is clear: a significant part of the global code will be scanned by AI in the near future. The models have become too effective at finding bugs that have been hidden for a long time for this evolution to be ignored. And with the rise of “vibe coding,” the trend where more and more code is generated by AI, the need for automated and intelligent scanning tools will only grow. The faster you generate code, the more the attack surface grows, and the more tools are needed that can secure these code bases at the same speed.
For businesses, the challenge is strategic. Those who incorporate these AI security tools into their processes now will get ahead of the curve. They will detect and fix vulnerabilities before attackers exploit them. Those who wait may find themselves late, facing attackers who will use AI to identify weaknesses even more quickly.
This is precisely the type of technological shift in which we support businesses at Scroll. Integrating Claude Code Security or other AI security tools into your development workflows doesn't happen at the push of a button. This requires a detailed understanding of your technical stack, your existing processes and your compliance constraints. If you want to anticipate this evolution and structure your approach to AI-assisted software security, contact the Scroll agency. We help technical teams make the most of these new capabilities, from the assessment phase to operational deployment.
Claude Code Security is an AI security tool developed by Anthropic, integrated with Claude Code on the web. It scans entire code bases for vulnerabilities that traditional static analysis tools don't see, then it suggests targeted fixes that are subject to human approval. Claude Code Security thinks about code like a security researcher: he traces data flows, understands interactions between components and identifies complex logical flaws. It is currently available as a research preview for Anthropic Enterprise and Team customers.
Claude Code Security detects several categories of vulnerabilities: memory corruption and buffer overflows, injection flaws such as SQL or command injections, authentication bypasses that allow authentication mechanisms to be bypassed, and complex logical errors related to access control or business logic. Using Claude Opus 4.6, Anthropic identified over 500 high-severity vulnerabilities in open source projects like Ghostscript, OpenSC, and CGIF.
Classic static analysis tools work by pattern matching: they compare code to a signature base of known vulnerabilities. Claude Code Security reasons in a contextual way about the code. It reads Git history, traces data flows through files, and understands business logic. Each result also involves an adversarial check where Claude questions his own discoveries to reduce false positives. Claude Code Security is designed as a complement to existing tools, not as a replacement.
Claude Code is based on a permission-based architecture that works in read-only mode by default. Any file changes or command execution require explicit approval. The bash order approval system automatically blocks suspicious orders. On the web, each session runs in an isolated virtual machine with file system and network isolation. Model Context Protocol (MCP) servers are subject to trust verification, and enterprise security policies cannot be bypassed by individual developers.
Claude Code Security has been available in limited research preview since February 2026. To access it, you must have an Anthropic Enterprise or Team plan and request access on the official product page. Maintainers of open source projects benefit from accelerated and free access. The tool can only be used on code that your company owns and on which it has all the necessary rights.


.svg)
.avif)








.svg)
.svg)
.svg)